Cloud Computing Security: Let’s Get Physical
Data center operators need to prevent against theft, tampering, and disasters. New hardware solutions that depend on connectors, sensors, and antennas, combined with software-level security, offer an unmistakable improvement over the old data center paradigm.

The current major trend in the evolution of IT infrastructure is the widespread migration of computing and storage resources from onsite data centers to the cloud. With this major shift, firms can easily spool up more capacity with a few clicks, rather than deploy a slow and costly investment in physical hardware in their own data centers. This shift is allowing companies to operate much more flexibly with the way they consume computing and storage resources, unlocking the sought-after business benefits of agility and scalability.
The widespread move to cloud computing has been underway for a few years, and in 2019 the topic on everyone’s minds is security. The cloud and hybrid onsite/cloud IT infrastructures in use today are much more complex than IT infrastructures were just a decade ago, and there is significant concern that yesterday’s security best practices are losing relevance. On the software side, firms like Aporeto and Twistlock are reinventing the classic approach to security based on IP addresses to overcome the problems increased infrastructural complexity poses. These are necessary developments, but hardware-level security has also changed tremendously in the cloud computing age.
In the past, companies usually administered the physical security of their data centers themselves. Today, these companies buy cloud computing resources from companies like Amazon and Microsoft, and probably have no idea where their data is being physically stored.
So how do big cloud providers like Amazon Web Services (AWS) ensure the physical security of their data centers? And what does having so much of a company’s data and computing in the cloud, including increasingly mission-critical applications, mean for the overall effectiveness of security?
Inherent in the migration to the cloud is the reality that more and more critical data is being stored physically in fewer and fewer places. This means that every company that buys cloud services from one of the major cloud providers has access to state-of-the-art security, both on the software side and on the physical side. Startup companies love the major cloud providers like AWS because they can buy only the capacity they need, and also have those computers physically protected by Amazon’s layers of security.
Amazon advertises that its data centers are protected by four layers of security: an environmental layer, where everything from sustainability to environmental risks are considered; the infrastructure layer, which makes accommodations for things like fires and power outages; the perimeter layer, which includes guards and fences; and the data layer, which includes advanced access controls for customer data.
This is clearly a level of site security that most startups would struggle to achieve on their own. However, while it’s true that these AWS data centers are far more physically secure, their number is limited. In spite of the environmental security layer, could a natural disaster or deliberate attack damage what is quickly becoming the backbone of companies’ ability to deliver digital services to its customers? Amazon contends that the possibility is remote, since its environmental security layer includes a backup system that ensures that a disaster impacting a single region wouldn’t take data offline.
Part of Amazon’s security strategy for AWS was to keep the location of its data centers under wraps. However, last fall WikiLeaks published the location of AWS data centers across the globe, potentially undermining that aspect of the physical security of the firm’s data centers.
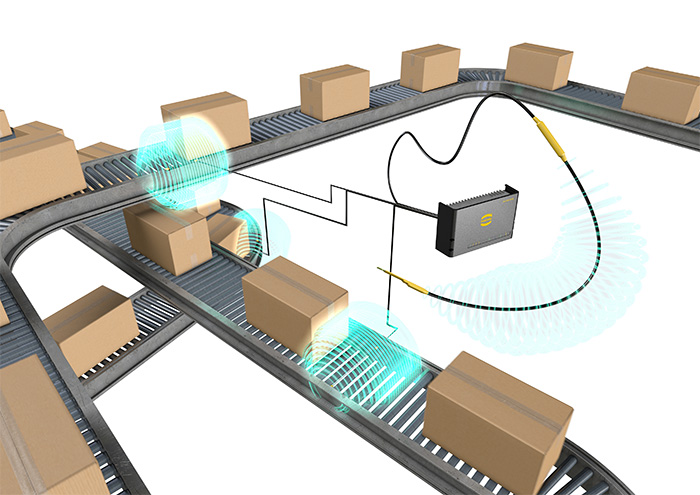
HARTING’s Ha-Vis LOCFIELD antenna, for use in RFID systems for data center asset management.
In the event of unauthorized access or tampering, or a disaster that damages equipment, companies need to carefully manage and track every piece of equipment in a data center. RFID technology is one way to monitor servers in real time, to prevent against unauthorized removal. A tag or transponder unit outfitted with an IC chip and antenna is attached to the equipment, and it will provide constant visibility and updates on the server’s status and location. HARTING’s Ha-Vis LOCFIELD antenna eliminates the need for patch antennas, as the coaxial antenna cable itself serves as an antenna. In data centers, this antenna can provide real-time monitoring from within server racks.

TE Connectivity’s AmbiMate MS4 Series sensor module
Amazon employs a host of security features to ensure security in its facilities, with a focus on physical access. Every entrance to server rooms is guarded by electronic control devices that require multi-factor authentication, and facilities are equipped with sensor-based security that can detect, for example, when a door is being held open too long. Machine vision-enabled security cameras capture and retain video footage of the entire facility. TE Connectivity’s AmbiMate MS4 Series sensor module can be used in connected building scenarios to monitor sound, light, movement, and other measures that indicate the movement of equipment and people.
Data centers can design in additional security at the server level by employing keyed connectors that feature unique keying details that prevent someone from disconnecting or switching cables in the fiber port. Keyed connectors guard against unauthorized or accidental tampering by preventing mated connections between opposing keys. Belden’s FiberExpress secure/keyed LC system and Brilliance keyed connectors protect data security by segregating specific segments of a network and making disruption to the physical network difficult. It is also challenging to reproduce the keying details, adding another physical layer of complexity to protect equipment.

Belden’s Brilliance keyed connectors guard against unauthorized or accidental tampering.
Cloud services firms like Amazon and Microsoft make it a goal to make cloud computing seem like magic to their customers, but as cloud capacity and services continue to expand, the demand for physical security and the cabling and components that come with it will grow.
Like this article? Check out our other New Technology, Data Center, and Cloud Computing articles, our 2019 Article Archive, and our Datacom/Telecom Market Page.
- 30 Years of Automotive CAN - March 30, 2021
- Industrial Interconnects Enable Advanced Process Controls in the Fresh Water Industry - February 23, 2021
- Remote Work Opens Network Infrastructures to Security Risks - December 8, 2020





